which of these are not risk factors for potential attackers 6 tips for reducing the risk of a fatal cyber attack infographic
If you are looking for 20 - Cyber Security Risk, threats and vulnerabilities Flashcards | Quizlet you've came to the right place. We have 10 Images about 20 - Cyber Security Risk, threats and vulnerabilities Flashcards | Quizlet like Attackers posing as legitimate insiders still an enormous security risk, Prevention: Risk & Protective Factors and also Solved Which of the following are potential attack vectors? | Chegg.com. Read more:
20 - Cyber Security Risk, Threats And Vulnerabilities Flashcards | Quizlet
 quizlet.com
quizlet.com
20 - Cyber Security Risk, threats and vulnerabilities Flashcards | Quizlet
Best Practices To Prevent The Risk Of Cyber Attacks | Cyber Solutions
 cds.thalesgroup.com
cds.thalesgroup.com
Best practices to prevent the risk of cyber attacks | Cyber Solutions ...
Solved Which Of The Following Are Potential Attack Vectors? | Chegg.com
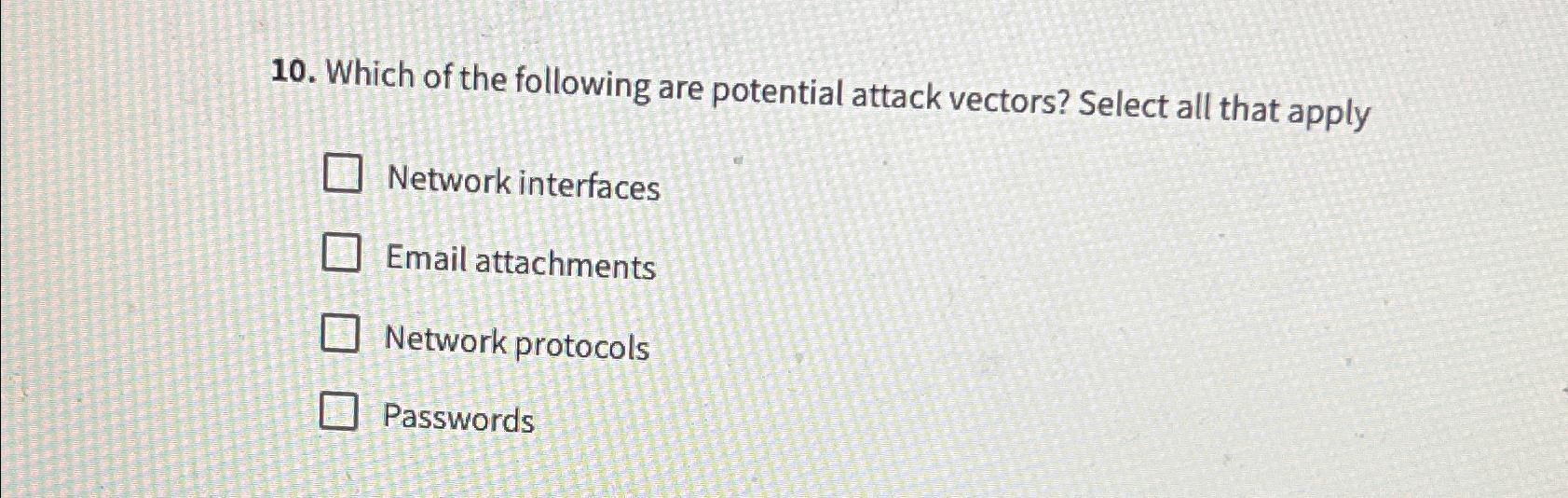 www.chegg.com
www.chegg.com
Solved Which of the following are potential attack vectors? | Chegg.com
6 Tips For Reducing The Risk Of A Fatal Cyber Attack Infographic
 blackcell.io
blackcell.io
6 Tips for Reducing the Risk of a Fatal Cyber Attack Infographic ...
Solved: Which Of The Following Could Be Targets Of Ransomware Attackers
Solved: Which of the following could be targets of ransomware attackers ...
Risk Analysis, Essential For Your Cybersecurity - MS Solutions
 mssolutions.ca
mssolutions.ca
Risk analysis, essential for your cybersecurity - MS Solutions
Dynamic Risk Assessment
 www.asisonline.org
www.asisonline.org
Dynamic Risk Assessment
No One’s Doing Risk Assessments Properly. Here’s Why. | SIS Industrial
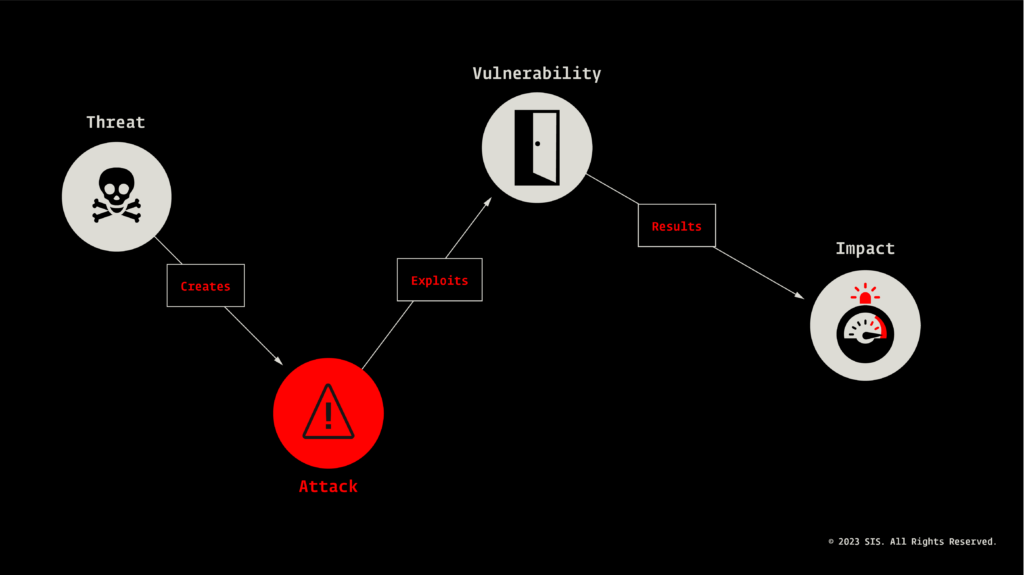 sis-ics.com
sis-ics.com
No one’s doing risk assessments properly. Here’s why. | SIS Industrial ...
Attackers Posing As Legitimate Insiders Still An Enormous Security Risk
 www.helpnetsecurity.com
www.helpnetsecurity.com
Attackers posing as legitimate insiders still an enormous security risk ...
Prevention: Risk & Protective Factors
 sharefactssavelives.org
sharefactssavelives.org
Prevention: Risk & Protective Factors
Solved which of the following are potential attack vectors?. Solved: which of the following could be targets of ransomware attackers .... Attackers posing as legitimate insiders still an enormous security risk